February
2020
Cyber security in M&A: a two-way relationship
There are at least two aspects in which the delicacy of M&A operations has to do with cyber security and both are now considered crucial for the deal’s success. The first aspect regards the focus that is put on the best practices for structuring the acquisition process: the IT platforms and tools for exchanging data and information in the negotiation, the sensitive data made available and the policies to access this data, bearing in mind that data is one of the company’s assets.
In the second aspect, it becomes crucial to evaluate the targeted company’s cyber security levels and what the risks are of data breach for the new business to be acquired. It is often necessary to carry out a cyber due diligence which, alongside financial, industrial and commercial analysis, detects risks in data management and IT security. The importance of cyber due diligence became clear to everyone three years ago, when Verizon lowered its offer to buy Yahoo's core business by 350 million dollars after the American search engine suffered two massive cyber-attacks.
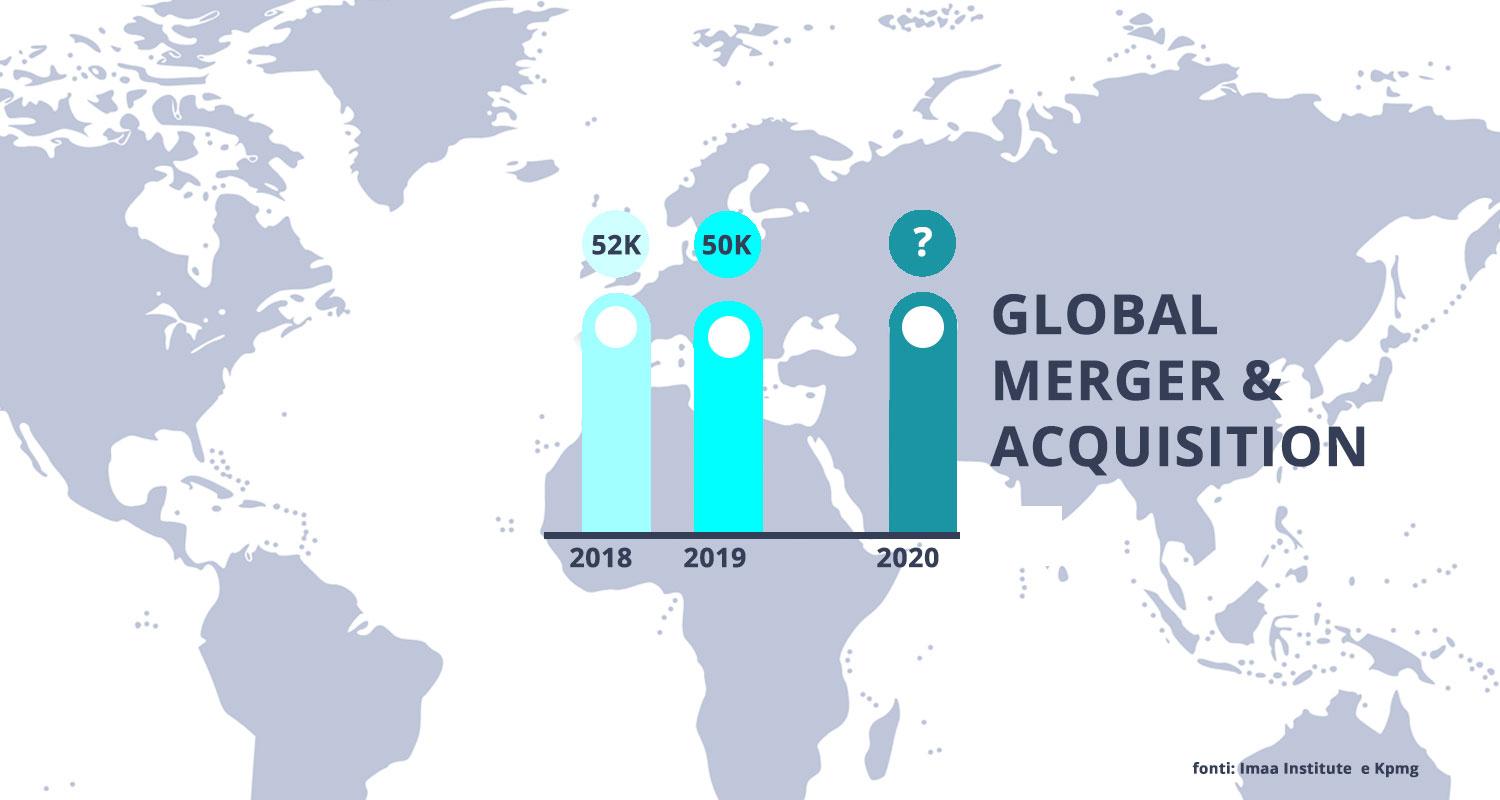
Mergers and acquisitions for 3700 billion dollars in 2019
In 2019, there were 50.000 mergers and acquisitions globally, compared to over 52.000 in the previous year, for a total value - calculated by the IMAA Institute (Institute for Mergers, Acquisitions and Alliances) - of approximately 3700 billion dollars (-10% compared to 2018). Europe represented more than a quarter of the transactions in value, which is approximately one trillion dollars, and a third in volume: in both cases there was a slight drop. Italy was disappointing: a thousand transactions, as in 2018, but for less than 38 billion euros (-60%), according to KPMG, with the sale of Magneti Marelli to the Japanese CK Holdings that represented the most important deal of the year (5.8 billion).
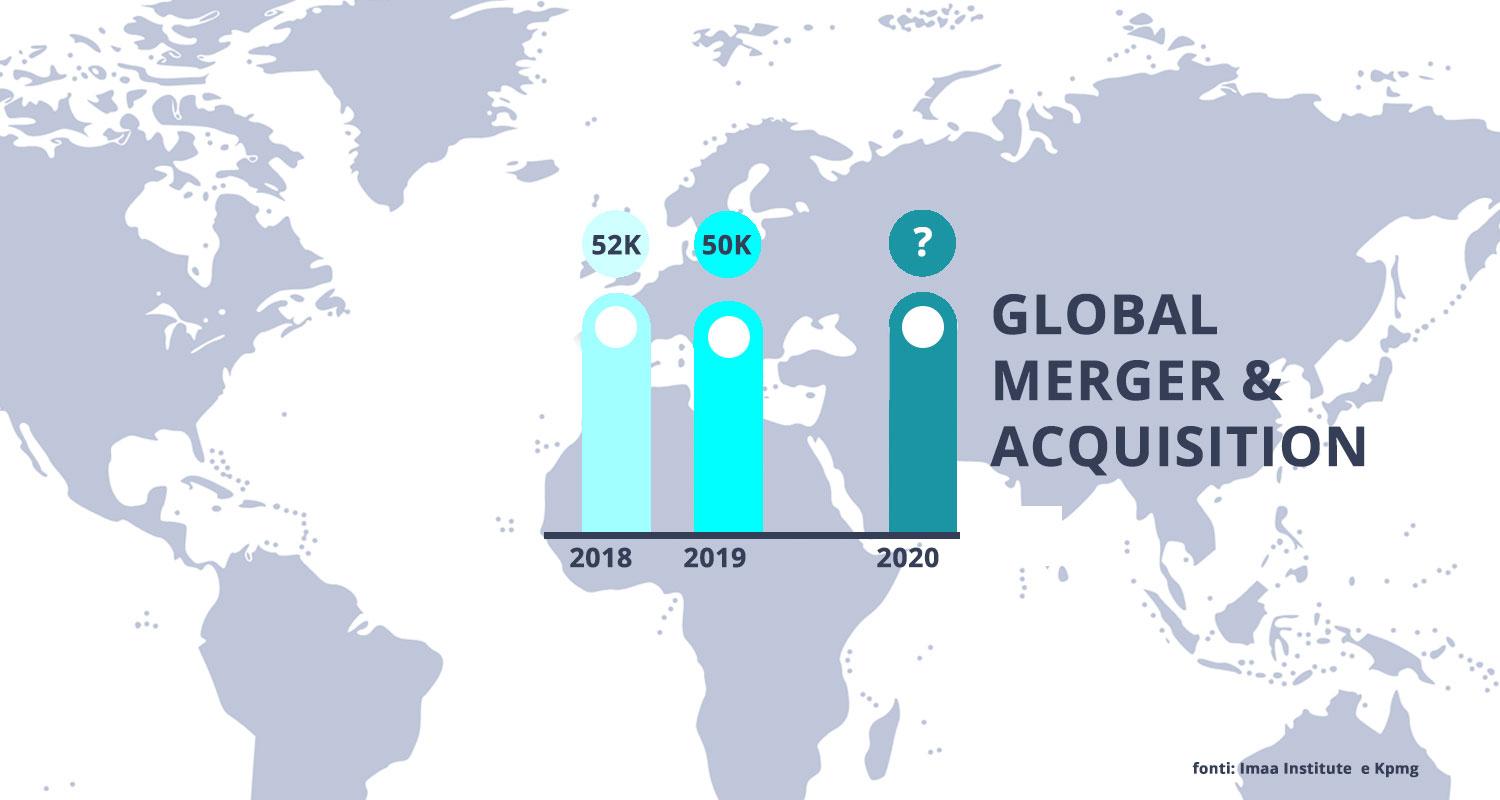
And 2020? Bailouts and nationalizations after Covid-19
2020 started slowly, but before the change of scenario due to the Covid-19 pandemic, it could have been the seventh consecutive year with a total value of operations exceeding 3 trillion dollars. After a quarter "sunk" by the lockdown in many key countries, the first statistics are clear: according to data collected by Refinitiv, in the United States the number of aggregate operations fell by 9% in the period January-March, but above all, the total value has halved to 250 billion dollars. Globally, in the same period, the contraction in terms of value was 28% for a value of 700 billion. After the forced stop, experts from the banking world and investment funds say that traditional M&A could still leave room for a large amount of rescue, restructuring or nationalization operations, partly as a consequence for the need to rebuild entire industrial sectors shocked by the impact of Coronavirus (for example the travel-transport sector), partly as a consequence of the intention of national governments to secure their major domestic industries or service companies.
VDRs: a market linked to M&A with double-digit growth
Even in a changed scenario, the growth trend of the technological and IT tools used in transactions will continue, starting with Virtual Data Rooms: some studies assign to the VDR market a global value already exceeding one billion dollars and with double-digit growth potential over the next ten years. The high development rate confirms the central role that these solutions represent when companies, private equity funds or other professional investors - together with their large teams of advisors - examine and negotiate an acquisition. On the one hand, for the operational need to work efficiently, thoroughly and multilaterally on documents, projections, contracts. On the other, because the negotiation phase hides drawbacks for data management: it exposes sensitive aspects of the organization, i.e. its data, to the risk of a violation and represents an important test of the company's good practices.
The provider chosen to deliver digital VDR solutions to support M&A operations also plays a central role if the objectives to be achieved and the risks to be avoided are clear. In mergers and acquisitions where a huge amount of sensitive documents are managed and shared, it is important for clients to have greater guarantees and resilience from the provider with respect to security and data control. For VDR providers, focusing on specific certifications and accreditations on secure and internationally recognized information management systems definitely makes the difference. Knowing in time whether the provider has proprietary servers or not and knowing where they are geographically located is, together with the availability of Business Continuity and Disaster Recovery close to real time, another strategic information to have.
Another cybersecurity aspect related to M&A involves not so much the acquisition process but rather its contents: a PWC report entitled "When cyber threatens M&A" quotes a Donnelley Financial Solutions/Mergermarket report to affirm that 80% of deal-makers at a global level found themselves faced with an unexpected problem related to data security in at least one out of four operations in the period 2015-17. If the Verizon-Yahoo case is sensational, it is wrong to think that these risks only concern the aggregations between technological groups. Another striking example was the acquisition of Starwood Hotels by Marriott: the latter, after taking over the competitor in 2016, later found out that there had been a theft of sensitive information belonging to 500 million Starwood customers started in 2014 and lasted until 2018.
A business’s degree of protection against data breaches and the impact that an event can have on the target company can also significantly change the assessment of an asset and allow to correctly consider the synergies between the two companies, starting from the cyber aspect: how much can the diversity of systems and protocols used slow down the integration of the two businesses once the merger has occurred and add unplanned costs in the industrial plan?